Windows Server 2008 R2 Unleashed (91 page)
Read Windows Server 2008 R2 Unleashed Online
Authors: Noel Morimoto

which clients could connect, download security patches, and install those patches.
Invoking the Windows Update web page remotely installed an executable, which ran a
test to see which hotfixes had been applied and which were needed, based on the
Microsoft components installed on the machine. Those that were not applied were offered
up for download, and users could easily install these patches.
Windows Update streamlined the security patch verification and installation process, but
the major drawback was that it required a manual effort to go up to the server every few
days or weeks and check for updates. A more efficient, automated process was required.
Deploying the Automatic Updates Client
The Automatic Updates client was developed to automate the installation of security fixes
and patches and to give users the option to automatically “drizzle” patches across the
Internet to the local computer for installation. Drizzling, also known as Background
Using Windows Server Update Services
435
Intelligent Transfer Service (BITS), is a process in which a computer intelligently utilizes
unused network bandwidth to download files to the machine. Because only unused band-
width is used, there is no perceived effect on the network client itself.
All currently supported versions of Microsoft clients include the Automatic Updates client
built in to the OS.
Understanding the Development of Windows Server Update Services
The Windows Update website and the associated client provided for the needs of most
13
home users and some small offices. However, large organizations, concerned about the
bandwidth effects of hundreds of machines downloading large numbers of updates over
the Internet, often disabled this service or discouraged its use. These organizations often
had a serious need for Windows Update’s capabilities. This fact led to the development of
Software Update Services (SUS), which was later improved into the new product, Windows
Server Update Services (WSUS).
WSUS started as a free download from Microsoft that effectively gives organizations their
own, independent version of the Windows Update server. The latest version of WSUS runs
on either a Windows Server 2003 SP1 or greater machine that is running Internet
Information Services. Clients connect to a central intranet WSUS server for all their secu-
ptg
rity patches and updates.
WSUS is not considered to be a replacement technology for existing software deployment
solutions such as System Center Configuration Manager (SCCM), but rather it is envi-
sioned as a solution for mid- to large-size businesses to take control over the fast deploy-
ment of security patches as they become available. It also offers a myriad of reports for
administrators.
Examining WSUS Prerequisites
Deploying WSUS on a dedicated server is preferable, but it can also be deployed on a
Windows Server 2008 R2 server that is running other tasks, as long as that server is
running Internet Information Services. The following list details the minimum levels of
hardware on which WSUS will operate:
. Windows Server 2003 SP1/SP2 or greater
. Internet Information Services (IIS)
. Background Intelligent Transfer Service (BITS)
. Windows Internal Database role or SQL Server 2005 installed locally or on a
remote server
. Microsoft .NET Framework 2.0 or greater
436
CHAPTER 13
Server-Level Security
Installing WSUS on a Windows Server 2008 R2 Server
The installation of WSUS is very easy, as it is installed as a server role from Server
Manager. The guided setup will install WSUS and any required components.
To complete the initial installation of WSUS, follow these steps:
1. Launch Server Manager.
2. In the Roles Summary pane, select Add Roles to start the wizard.
3. Click Next.
4. Select Windows Server Update Services, and click Next.
5. The Add Role Services and Features Required for Windows Server Update Services
window prompts for additional components to install, if necessary. Required compo-
nents are the Web Server (IIS) web server and management tools, the Windows
Process Activation Service Process Model, and the .NET environment. Click Add
Required Role Services to continue.
6. Click Next.
7. Read the Introduction to Web Server (IIS) overview, and click Next.
8. Click Next to select the default role services to install for Web Server (IIS).
ptg
9. Read the Introduction to Windows Server Update Services overview, and click Next.
10. Read the summary of installation selections, and click Install.
11. Server Manager shows “Searching for Updates” and “Downloading” while it connects
to the Microsoft download site and downloads the most recent version of WSUS. It
also installs Web Services (IIS) and the Windows Process Activation Service, if needed.
12. The Windows Server Update Services Setup Wizard displays during the installation
progress. Click Next.
13. Read and accept the license agreement, and click Next.
14. If prompted that Report Viewer 2005 is not installed, click Next to continue (certain
reports will be unavailable without this downloadable add-on).
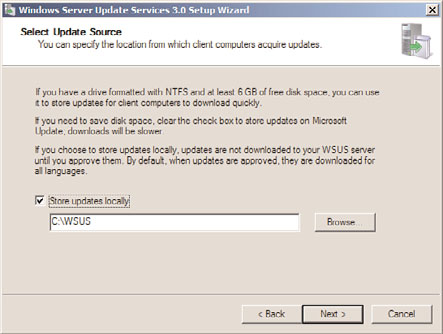
15. Check the Store Updates Locally check box, and enter a location in which to store
them, as shown in Figure 13.11. This location must be large enough to hold a large
number of downloadable patches. Click Next to continue.
16. Select Install the Windows Internal Database on This Computer or Use an Existing
Database Server on a Remote Computer if you want to use an external SQL server.
17. Select to Use the Existing IIS Web Site. Click Next to continue.
18. Click Next after reviewing the settings on the Ready to Install page.
19. The installation completes in Server Manager and, after the Finish button is clicked,
the WSUS Configuration Wizard is displayed. Read the information and click Next.
20. Click Next to join the Microsoft Update Improvement Program.
21. Select Synchronize from Microsoft Update, and click Next.
22. Configure your proxy server settings, if necessary, and click Next.
Using Windows Server Update Services
437
13
FIGURE 13.11
Installing WSUS.
23. Click Start Connecting to save settings and download update information. This
might take several minutes. Click Next.
24. Select the update language(s), and click Next.
ptg
25. Select the products for which you want updates, and click Next.
26. Select the classifications of updates you want to download, and click Next.
27. Configure the schedule that you want WSUS to synchronize with the Microsoft
Update servers or select Synchronize Manually. Click Next.
28. Ensure that Begin Initial Synchronization is selected, and click Finish.
29. Review the installation results, click Close, and close Server Manager.
WSUS administration is performed from the WSUS MMC. This console is the main loca-
tion for all configuration settings for WSUS and is the sole administrative console. It can
be accessed from Administrative Tools, Microsoft Windows Server Update Services 3.0 SP1,
or directly from Server Manager.
Automatically Configuring Clients via Group Policy
The configuration of the Automatic Updates client included with all current versions of
Windows can be streamlined by using a group policy in an Active Directory environ-
ment. Windows Server 2008 R2 domain controllers automatically contain the proper
Windows Update Group Policy extension, and a group policy can be defined by following
these steps:
1. Open Group Policy Management (Start, All Programs, Administrative Tools, Group
Policy Management).
438
CHAPTER 13
Server-Level Security
2. Navigate to the organizational unit that will have the group policy applied, right-
click the name of the organizational unit, and choose Create a GPO in This Domain,
and Link It Here.
3. Enter a name for the GPO, such as WSUS GPO. You also have the option to start
from the settings of an existing GPO. Click OK.
4. Right-click on the newly created GPO, and select Edit to invoke the Group Policy
Management Editor.
5. Expand the Group Policy Management Editor to Computer Configuration\
Policies\Administrative Templates\Windows Components\Windows Update.
6. Double-click the Configure Automatic Updates setting.
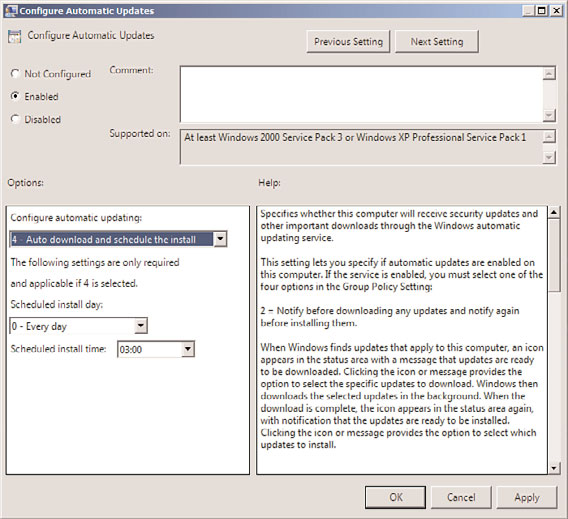
7. Set the group policy to be enabled, and configure the automatic updating sequence
as desired. The three options given—2, 3, and 4—allow for specific degrees of client
intervention. For seamless, client-independent installation, choose option 4, as
shown in Figure 13.12.
ptg
FIGURE 13.12
Configuring Windows Update Group Policy settings.
8. Schedule the interval that updates will be installed, bearing in mind that some
updates require reboots.
Using Windows Server Update Services
439
9. Click Next Setting to configure more options.
10. Click Enabled to specify the web location of the WSUS server. Entering the fully
qualified domain name of the server is recommended. Enter both settings (usually
the same server), and click OK to save the Group Policy settings. Click Next Setting.
NOTE
Organizations that choose to use a custom web IIS website are required to use Port
8530 for client access to WSUS. In this case, enter the web location with the port
number, such as http://sfwsus.companyabc.com:8530, for both settings.
13
11. Enter how often the client checks for updates, and then click Next Setting.
12. Review the remaining option settings and configure as desired. Click OK when you
are finished.
13. Repeat the procedure for any additional organizational units. (The same group policy
can be linked in more than one location.)
NOTE
ptg
Organizations that do not use Active Directory or group policies have to manually config-
ure each client’s settings to include the location of the WSUS server. This can be done
through a local policy or manually through Registry settings, as defined in the WSUS Help.
Deploying Security Patches with WSUS
Depending on the settings chosen by the group policy or the Registry, the clients that are
managed by WSUS automatically download updates throughout the day and install them
at a specified time. Some computers might be configured to allow for local interaction,
scheduling proper times for the installation to take place and prompting for “drizzle”
downloading.
Clients that are configured to use WSUS are not prompted to configure their Automatic
Update settings, and they are grayed out to prevent any changes from occurring. Users
without local administrative access cannot make any changes to the installation schedule,
although local admin users can postpone forced installs.
NOTE
Generally, it is good practice to allow servers to control the download and installation
schedule, but to force clients to do both automatically. Depending on the political cli-
mate of an organization, this might or might not be a possibility.
440
CHAPTER 13
Server-Level Security
Out of the box, Windows Server 2008 R2 is by far the most secure Windows yet. Increased
security emphasis through the Trustworthy Computing initiative helps to increase overall
