The Code Book (34 page)

Table 12
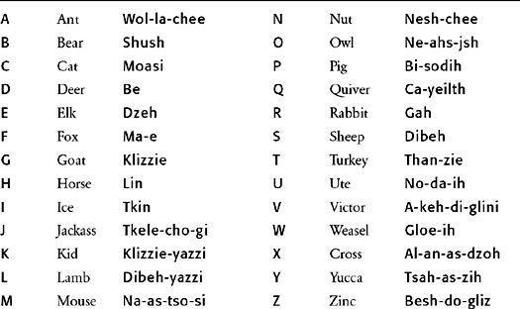
The Navajo alphabet code.
Japanese forces had attacked Pearl Harbor on December 7, 1941, and not long after they dominated large parts of the western Pacific. Japanese troops overran the American garrison on Guam on December 10, they took Guadalcanal, one of the islands in the Solomon chain, on December 13, Hong Kong capitulated on December 25, and U.S. troops on the Philippines surrendered on January 2, 1942. The Japanese planned to consolidate their control of the Pacific the following summer by building an airfield on Guadalcanal, creating a base for bombers which would enable them to destroy Allied supply lines, thus making any Allied counterattack almost impossible. Admiral Ernest King, Chief of American Naval Operations, urged an attack on the island before the airfield was completed, and on August 7, the 1st Marine Division spearheaded an invasion of Guadalcanal. The initial landing parties included the first group of code talkers to see action.
Although the Navajos were confident that their skills would be a blessing to the marines, their first attempts generated only confusion. Many of the regular signal operators were unaware of this new code, and they sent panic messages all over the island, stating that the Japanese were broadcasting on American frequencies. The colonel in charge immediately halted Navajo communications until he could convince himself that the system was worth pursuing. One of the code talkers recalled how the Navajo code was eventually brought back into service:

Figure 52
The first 29 Navajo code talkers pose for a traditional graduation photograph. (
photo credit 5.1
)
The colonel had an idea. He said he would keep us on one condition: that I could outrace his “white code”—a mechanical ticking cylinder thing. We both sent messages, by white cylinder and by my voice. Both of us received answers and the race was to see who could decode his answer first. I was asked, “How long will it take you? Two hours?” “More like two minutes,” I answered. The other guy was still decoding when I got the roger on my return message in about four and a half minutes. I said, “Colonel, when are you going to give up on that cylinder thing?” He didn’t say anything. He just lit up his pipe and walked away.
The code talkers soon proved their worth on the battlefield. During one episode on the island of Saipan, a battalion of marines took over positions previously held by Japanese soldiers, who had retreated. Suddenly a salvo exploded nearby. They were under friendly fire from fellow Americans who were unaware of their advance. The marines radioed back in English explaining their position, but the salvos continued because the attacking American troops suspected that the messages were from Japanese impersonators trying to fool them. It was only when a Navajo message was sent that the attackers saw their mistake and halted the assault. A Navajo message could never be faked, and could always be trusted.
The reputation of the code talkers soon spread, and by the end of 1942 there was a request for 83 more men. The Navajo were to serve in all six Marine Corps divisions, and were sometimes borrowed by other American forces. Their war of words soon turned the Navajos into heroes. Other soldiers would offer to carry their radios and rifles, and they were even given personal bodyguards, partly to protect them from their own comrades. On at least three occasions code talkers were mistaken for Japanese soldiers and captured by fellow Americans. They were released only when colleagues from their own battalion vouched for them.
The impenetrability of the Navajo code was all down to the fact that Navajo belongs to the Na-Dene family of languages, which has no link with any Asian or European language. For example, a Navajo verb is conjugated not solely according to its subject, but also according to its object. The verb ending depends on which category the object belongs to: long (e.g., pipe, pencil), slender and flexible (e.g., snake, thong), granular (e.g., sugar, salt), bundled (e.g., hay), viscous (e.g., mud, feces) and many others. The verb will also incorporate adverbs, and will reflect whether or not the speaker has experienced what he or she is talking about, or whether it is hearsay. Consequently, a single verb can be equivalent to a whole sentence, making it virtually impossible for foreigners to disentangle its meaning.
Despite its strengths, the Navajo code still suffered from two significant flaws. First, words that were neither in the natural Navajo vocabulary nor in the list of 274 authorized codewords had to be spelled out using the special alphabet. This was time-consuming, so it was decided to add another 234 common terms to the lexicon. For example, nations were given Navajo nicknames: “Rolled Hat” for Australia, “Bounded by Water” for Britain, “Braided Hair” for China, “Iron Hat” for Germany, “Floating Land” for the Philippines, and “Sheep Pain” for Spain.
The second problem concerned those words that would still have to be spelled out. If it became clear to the Japanese that words were being spelled out, they would realize that they could use frequency analysis to identify which Navajo words represented which letters. It would soon become obvious that the most commonly used word was dzeh, which means “elk” and which represents e, the most commonly used letter of the English alphabet. Just spelling out the name of the island Guadalcanal and repeating the word wol-la-chee (ant) four times would be a big clue as to what word represented the letter a. The solution was to add more words to act as extra substitutes (homophones) for the commonly used letters. Two extra words were introduced as alternatives for each of the six commonest letters (e, t, a, o, i, n), and one extra word for the six next commonest letters (s, h, r, d, l, u). The letter a, for example, could now also be substituted by the words be-la-sana (apple) or tse-nihl (axe). Thereafter, Guadalcanal could be spelled with only one repetition: klizzie, shi-da, wol-la-chee, lha-cha-eh, be-la-sana, dibeh-yazzie, moasi, tse-nihl, nesh-chee, tse-nihl, ah-jad (goat, uncle, ant, dog, apple, lamb, cat, axe, nut, axe, leg).
As the war in the Pacific intensified, and as the Americans advanced from the Solomon Islands to Okinawa, the Navajo code talkers played an increasingly vital role. During the first days of the attack on Iwo Jima, more than eight hundred Navajo messages were sent, all without error. According to Major General Howard Conner, “without the Navajos, the marines would never have taken Iwo Jima.” The contribution of the Navajo code talkers is all the more remarkable when you consider that, in order to fulfill their duties, they often had to confront and defy their own deeply held spiritual fears. The Navajo believe that the spirits of the dead,
chindi
, will seek revenge on the living unless ceremonial rites are performed on the body. The war in the Pacific was particularly bloody, with corpses strewn across the battlefields, and yet the code talkers summoned up the courage to carry on regardless of the
chindi
that haunted them. In Doris Paul’s book
The Navajo Code Talkers
, one of the Navajo recounts an incident which typifies their bravery, dedication and composure:

Figure 53
Corporal Henry Bake, Jr. (left) and Private First Class George H. Kirk using the Navajo code in the dense jungles of Bougainville in 1943.
If you so much as held up your head six inches you were gone, the fire was so intense. And then in the wee hours, with no relief on our side or theirs, there was a dead standstill. It must have gotten so that this one Japanese couldn’t take it anymore. He got up and yelled and screamed at the top of his voice and dashed over our trench, swinging a long samurai sword. I imagine he was shot from 25 to 40 times before he fell.
There was a buddy with me in the trench. But that Japanese had cut him across the throat, clear through to the cords on the back of his neck. He was still gasping through his windpipe. And the sound of him trying to breathe was horrible. He died, of course. When the Jap struck, warm blood spattered all over my hand that was holding a microphone. I was calling in code for help. They tell me that in spite of what happened, every syllable of my message came through.
Altogether, there were 420 Navajo code talkers. Although their bravery as fighting men was acknowledged, their special role in securing communications was classified information. The government forbade them to talk about their work, and their unique contribution was not made public. Just like Turing and the cryptanalysts at Bletchley Park, the Navajo were ignored for decades. Eventually, in 1968, the Navajo code was declassified, and the following year the code talkers held their first reunion. Then, in 1982, they were honored when the U.S. Government named August 14 “National Navajo Code Talkers Day.” However, the greatest tribute to the work of the Navajo is the simple fact that their code is one of very few throughout history that was never broken. Lieutenant General Seizo Arisue, the Japanese chief of intelligence, admitted that, although they had broken the American Air Force code, they had failed to make any impact on the Navajo code.
Deciphering Lost Languages and Ancient Scripts
The success of the Navajo code was based largely on the simple fact that the mother tongue of one person is utterly meaningless to anybody unacquainted with it. In many ways, the task that confronted Japanese cryptanalysts is similar to that which is faced by archaeologists attempting to decipher a long-forgotten language, perhaps written in an extinct script. If anything, the archaeological challenge is much more severe. For example, while the Japanese had a continuous stream of Navajo words which they could attempt to identify, the information available to the archaeologist can sometimes be just a small collection of clay tablets. Furthermore, the archaeological codebreaker often has no idea of the context or contents of an ancient text, clues which military codebreakers can normally rely on to help them crack a cipher.
Deciphering ancient texts seems an almost hopeless pursuit, yet many men and women have devoted themselves to this arduous enterprise. Their obsession is driven by the desire to understand the writings of our ancestors, allowing us to speak their words and catch a glimpse of their thoughts and lives. Perhaps this appetite for cracking ancient scripts is best summarized by Maurice Pope, the author of
The Story of Decipherment:
“Decipherments are by far the most glamorous achievements of scholarship. There is a touch of magic about unknown writing, especially when it comes from the remote past, and a corresponding glory is bound to attach itself to the person who first solves its mystery.”
The decipherment of ancient scripts is not part of the ongoing evolutionary battle between codemakers and codebreakers, because, although there are codebreakers in the shape of archaeologists, there are no codemakers. That is to say, in most cases of archaeological decipherment there was no deliberate attempt by the original scribe to hide the meaning of the text. The remainder of this chapter, which is a discussion of archaeological decipherments, is therefore a slight detour from the book’s main theme. However, the principles of archaeological decipherment are essentially the same as those of conventional military cryptanalysis. Indeed, many military codebreakers have been attracted by the challenge of unraveling an ancient script. This is probably because archaeological decipherments make a refreshing change from military codebreaking, offering a purely intellectual puzzle rather than a military challenge. In other words, the motivation is curiosity rather than animosity.
