The Code Book (12 page)

Next, he hit upon the idea that each number might represent a pair of letters, or a
digraph
. There are only 26 individual letters, but there are 676 possible pairs of letters, and this is roughly equal to the variety of numbers in the ciphertexts. Bazeries attempted a decipherment by looking for the most frequent numbers in the ciphertexts (22, 42, 124, 125 and 341), assuming that these probably stood for the commonest French digraphs (es, en, ou, de, nt). In effect, he was applying frequency analysis at the level of pairs of letters. Unfortunately, again after months of work, this theory also failed to yield any meaningful decipherments.
Bazeries must have been on the point of abandoning his obsession, when a new line of attack occurred to him. Perhaps the digraph idea was not so far from the truth. He began to consider the possibility that each number represented not a pair of letters, but rather a whole syllable. He attempted to match each number to a syllable, the most frequently occurring numbers presumably representing the commonest French syllables. He tried various tentative permutations, but they all resulted in gibberish—until he succeeded in identifying one particular word. A cluster of numbers (124-22-125-46-345) appeared several times on each page, and Bazeries postulated that they represented les-en-ne-mi-s, that is, “les ennemis.” This proved to be a crucial breakthrough.
Bazeries was then able to continue by examining other parts of the ciphertexts where these numbers appeared within different words. He then inserted the syllabic values derived from “les ennemis,” which revealed parts of other words. As crossword addicts know, when a word is partly completed it is often possible to guess the remainder of the word. As Bazeries completed new words, he also identified further syllables, which in turn led to other words, and so on. Frequently he would be stumped, partly because the syllabic values were never obvious, partly because some of the numbers represented single letters rather than syllables, and partly because the Rossignols had laid traps within the cipher. For example, one number represented neither a syllable nor a letter, but instead deviously deleted the previous number.
When the decipherment was eventually completed, Bazeries became the first person for two hundred years to witness the secrets of Louis XIV. The newly deciphered material fascinated historians, who focused on one tantalizing letter in particular. It seemed to solve one of the great mysteries of the seventeenth century: the true identity of the Man in the Iron Mask.
The Man in the Iron Mask has been the subject of much speculation ever since he was first imprisoned at the French fortress of Pignerole in Savoy. When he was transferred to the Bastille in 1698, peasants tried to catch a glimpse of him, and variously reported him as being short or tall, fair or dark, young or old. Some even claimed that he was a she. With so few facts, everyone from Voltaire to Benjamin Franklin concocted their own theory to explain the case of the Man in the Iron Mask. The most popular conspiracy theory relating to the Mask (as he is sometimes called) suggests that he was the twin of Louis XIV, condemned to imprisonment in order to avoid any controversy over who was the rightful heir to the throne. One version of this theory argues that there existed descendants of the Mask and an associated hidden royal bloodline. A pamphlet published in 1801 said that Napoleon himself was a descendant of the Mask, a rumor which, since it enhanced his position, the emperor did not deny.
The myth of the Mask even inspired poetry, prose and drama. In 1848 Victor Hugo had begun writing a play entitled
Twins
, but when he found that Alexandre Dumas had already plumped for the same plot, he abandoned the two acts he had written. Ever since, it has been Dumas’s name that we associate with the story of the Man in the Iron Mask. The success of his novel reinforced the idea that the Mask was related to the king, and this theory has persisted despite the evidence revealed in one of Bazeries’s decipherments.
Bazeries had deciphered a letter written by François de Louvois, Louis XIV’s Minister of War, which began by recounting the crimes of Vivien de Bulonde, the commander responsible for leading an attack on the town of Cuneo, on the French-Italian border. Although he was ordered to stand his ground, Bulonde became concerned about the arrival of enemy troops from Austria and fled, leaving behind his munitions and abandoning many of his wounded soldiers. According to the Minister of War, these actions jeopardized the whole Piedmont campaign, and the letter made it clear that the king viewed Bulonde’s actions as an act of extreme cowardice:
His Majesty knows better than any other person the consequences of this act, and he is also aware of how deeply our failure to take the place will prejudice our cause, a failure which must be repaired during the winter. His Majesty desires that you immediately arrest General Bulonde and cause him to be conducted to the fortress of Pignerole, where he will be locked in a cell under guard at night, and permitted to walk the battlements during the day with a mask.
This was an explicit reference to a masked prisoner at Pignerole, and a sufficiently serious crime, with dates that seem to fit the myth of the Man in the Iron Mask. Does this solve the mystery? Not surprisingly, those favoring more conspiratorial solutions have found flaws in Bulonde as a candidate. For example, there is the argument that if Louis XIV was actually attempting to secretly imprison his unacknowledged twin, then he would have left a series of false trails. Perhaps the encrypted letter was meant to be deciphered. Perhaps the nineteenth-century codebreaker Bazeries had fallen into a seventeenth-century trap.
The Black Chambers
Reinforcing the monoalphabetic cipher by applying it to syllables or adding homophones might have been sufficient during the 1600s, but by the 1700s cryptanalysis was becoming industrialized, with teams of government cryptanalysts working together to crack many of the most complex monoalphabetic ciphers. Each European power had its own so-called Black Chamber, a nerve center for deciphering messages and gathering intelligence. The most celebrated, disciplined and efficient Black Chamber was the Geheime Kabinets-Kanzlei in Vienna.
It operated according to a rigorous timetable, because it was vital that its nefarious activities should not interrupt the smooth running of the postal service. Letters which were supposed to be delivered to embassies in Vienna were first routed via the Black Chamber, arriving at 7
A.M.
Secretaries melted seals, and a team of stenographers worked in parallel to make copies of the letters. If necessary, a language specialist would take responsibility for duplicating unusual scripts. Within three hours the letters had been resealed in their envelopes and returned to the central post office, so that they could be delivered to their intended destination. Mail merely in transit through Austria would arrive at the Black Chamber at 10
A.M.
, and mail leaving Viennese embassies for destinations outside Austria would arrive at 4
P.M
. All these letters would also be copied before being allowed to continue on their journey. Each day a hundred letters would filter through the Viennese Black Chamber.
The copies were passed to the cryptanalysts, who sat in little kiosks, ready to tease out the meanings of the messages. As well as supplying the emperors of Austria with invaluable intelligence, the Viennese Black Chamber sold the information it harvested to other powers in Europe. In 1774 an arrangement was made with Abbot Georgel, the secretary at the French Embassy, which gave him access to a twice-weekly package of information in exchange for 1,000 ducats. He then sent these letters, which contained the supposedly secret plans of various monarchs, straight to Louis XV in Paris.
The Black Chambers were effectively making all forms of monoalphabetic cipher insecure. Confronted with such professional cryptanalytic opposition, cryptographers were at last forced to adopt the more complex but more secure Vigenère cipher. Gradually, cipher secretaries began to switch to using polyalphabetic ciphers. In addition to more effective cryptanalysis, there was another pressure that was encouraging the move toward securer forms of encryption: the development of the telegraph, and the need to protect telegrams from interception and decipherment.
Although the telegraph, together with the ensuing telecommunications revolution, came in the nineteenth century, its origins can be traced all the way back to 1753. An anonymous letter in a Scottish magazine described how a message could be sent across large distances by connecting the sender and receiver with 26 cables, one for each letter of the alphabet. The sender could then spell out the message by sending pulses of electricity along each wire. For example, to spell out hello, the sender would begin by sending a signal down the h wire, then down the e wire, and so on. The receiver would somehow sense the electrical current emerging from each wire and read the message. However, this “expeditious method of conveying intelligence,” as the inventor called it, was never constructed, because there were several technical obstacles that had to be overcome.
For example, engineers needed a sufficiently sensitive system for detecting electrical signals. In England, Sir Charles Wheatstone and William Fothergill Cooke built detectors from magnetized needles, which would be deflected in the presence of an incoming electric current. By 1839, the Wheatstone-Cooke system was being used to send messages between railway stations in West Drayton and Paddington, a distance of 29 km. The reputation of the telegraph and its remarkable speed of communication soon spread, and nothing did more to popularize its power than the birth of Queen Victoria’s second son, Prince Alfred, at Windsor on August 6, 1844. News of the birth was telegraphed to London, and within the hour
The Times
was on the streets announcing the news. It credited the technology that had enabled this feat, mentioning that it was “indebted to the extraordinary power of the Electro-Magnetic Telegraph.” The following year, the telegraph gained further fame when it helped capture John Tawell, who had murdered his mistress in Slough, and who had attempted to escape by jumping on to a London-bound train. The local police telegraphed Tawell’s description to London, and he was arrested as soon as he arrived at Paddington.
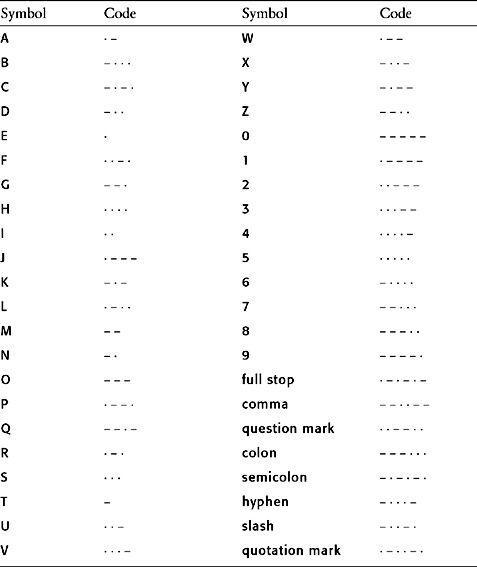
Meanwhile, in America, Samuel Morse had just built his first telegraph line, a system spanning the 60 km between Baltimore and Washington. Morse used an electromagnet to enhance the signal, so that upon arriving at the receiver’s end it was strong enough to make a series of short and long marks, dots and dashes, on a piece of paper. He also developed the now familiar Morse code for translating each letter of the alphabet into a series of dots and dashes, as given in
Table 6
. To complete his system he designed a sounder, so that the receiver would hear each letter as a series of audible dots and dashes.
Back in Europe, Morse’s approach gradually overtook the Wheatstone-Cooke system in popularity, and in 1851 a European form of Morse code, which included accented letters, was adopted throughout the Continent. As each year passed, Morse code and the telegraph had an increasing influence on the world, enabling the police to capture more criminals, helping newspapers to bring the very latest news, providing valuable information for businesses, and allowing distant companies to make instantaneous deals.
However, guarding these often sensitive communications was a major concern. The Morse code itself is not a form of cryptography, because there is no concealment of the message. The dots and dashes are merely a convenient way to represent letters for the telegraphic medium; Morse code is effectively nothing more than an alternative alphabet. The problem of security arose primarily because anyone wanting to send a message would have to deliver it to a Morse code operator, who would then have to read it in order to transmit it. The telegraph operators had access to every message, and hence there was a risk that one company might bribe an operator in order to gain access to a rival’s communications. This problem was outlined in an article on telegraphy published in 1853 in England’s
Quarterly Review:
Means should also be taken to obviate one great objection, at present felt with respect to sending private communications by telegraph—the violation of all secrecy—for in any case half-a-dozen people must be cognizant of every word addressed by one person to another. The clerks of the English Telegraph Company are sworn to secrecy, but we often write things that it would be intolerable to see strangers read before our eyes. This is a grievous fault in the telegraph, and it must be remedied by some means or other.
The solution was to encipher a message before handing it to the telegraph operator. The operator would then turn the ciphertext into Morse code before transmitting it. As well as preventing the operators from seeing sensitive material, encryption also stymied the efforts of any spy who might be tapping the telegraph wire. The polyalphabetic Vigenère cipher was clearly the best way to ensure secrecy for important business communications. It was considered unbreakable, and became known as
le chiffre indéchiffrable
. Cryptographers had, for the time being at least, a clear lead over the cryptanalysts.
Table 6
International Morse Code symbols.